AstraZeneca reportedly hit by serious cyberattack
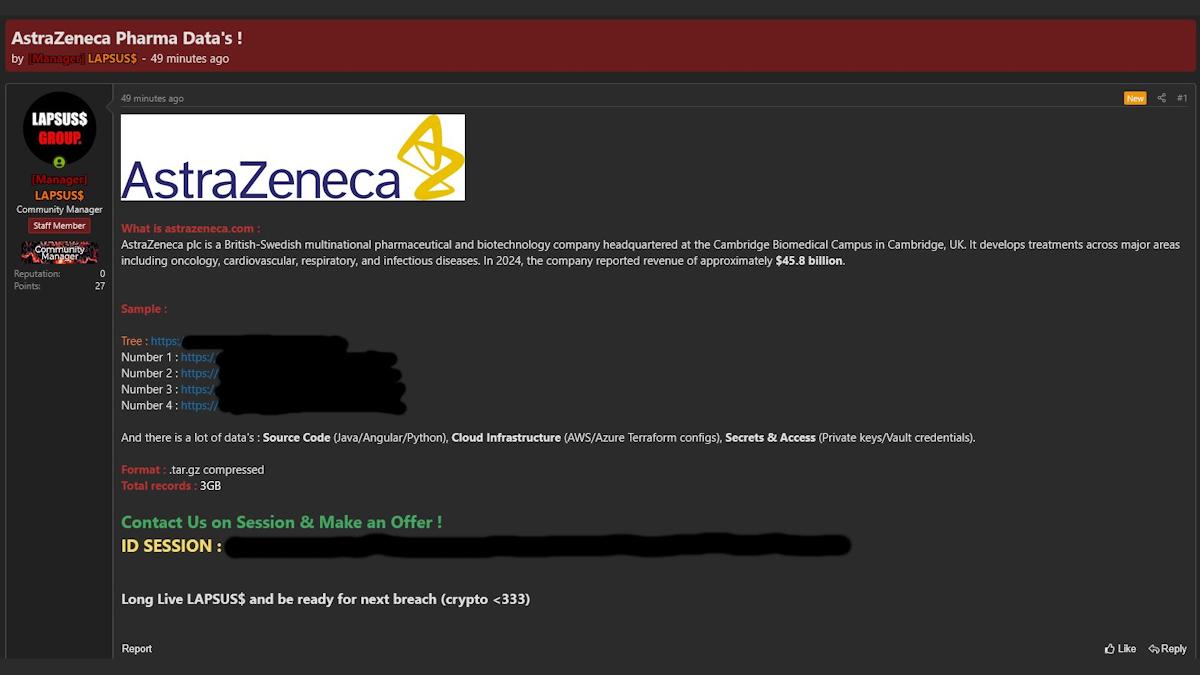
Screen shot of LAPSUS$ offer on Dark Web
A hacking group claims to have broken into AstraZeneca's IT systems and stolen confidential data, which they are now offering for sale.
The group, known as LAPSUS$, maintain that they have stolen around 3GB of compressed AZ data, but somewhat unusually are trying to sell it on the Dark Web rather than threatening to release it publicly in an attempt to extort money from AZ to keep it under wraps.
The pharma group has not commented on the claims by the hackers, who say the exfiltrated information includes source code, cloud infrastructure, employee-linked records, and private keys and other credentials for accessing systems, with samples released to help would-be buyers validate their authenticity. There is reportedly no customer data in the haul.
Cybersecurity specialist SOCRadar said that, if the claims are verified, "this could become one of the more serious cyber events to hit the healthcare sector this year."
"Even when infrastructure files do not contain live secrets, they can still give attackers useful insight into architecture, naming conventions, deployment logic, and service dependencies."
From a look at the sample data, SOCRadar analysts suggest that one of the samples appears to map internal identifiers to corporate email addresses, while a separate file structure indicates permission and wiki access workflows may also be included.
"This matters because identity and access information can be operationally valuable to attackers even when passwords are not directly exposed. It can help with phishing, privilege mapping, social engineering, and targeting internal systems."
The experts also note that the data could leave AZ vulnerable to additional intrusion attacks, and recommend that the company and others in the healthcare sector monitor "both initial access signals and Dark Web monetisation activity at the same time."
They add: "As this story develops, the key question will be whether the leaked material proves authentic at scale and whether the incident expands into broader extortion, disclosure, or follow-on compromise activity."
The breach marks another evolution of the tactics used by commercially-motivated hackers as they target enterprises, moving beyond the ransomware-based denial of service attacks that have hit pharma companies in the past, notably the 2017 NotPetya attack on MSD/Merck & Co, which is estimated to have cost the group around $1.4 billion to resolve.
Healthcare and life sciences companies have become targets for hackers because their data often includes high-value assets, including valuable R&D intellectual property, trade secrets, and sensitive employee and partner information.
Meanwhile, geopolitical tensions like the US-Israeli war on Iran have also led to attacks on healthcare companies by state-backed groups. Earlier this month, an Iranian hacker group claimed responsibility for a cyberattack against US medtech company Stryker, saying it was in retaliation for the bombing of the Minab school in Iran by US forces that killed 168 people, including 110 children.